Threat actors are actively exploiting critical vulnerabilities in OpenMetadata to gain unauthorized access to Kubernetes workloads and leverage them for cryptocurrency mining activity.
That’s according to the Microsoft Threat Intelligence team, which said the flaws have been weaponized since the start of April 2024.
OpenMetadata is an open-source platform that operates as a metadata management tool, offering a unified solution for data asset discovery, observability, and governance.
The flaws in question – all discovered and credited to security researcher Alvaro Muñoz – are listed below –
- CVE-2024-28847 (CVSS score: 8.8) – A Spring Expression Language (SpEL) injection vulnerability in PUT /api/v1/events/subscriptions (fixed in version 1.2.4)
- CVE-2024-28848 (CVSS score: 8.8) – A SpEL injection vulnerability in GET /api/v1/policies/validation/condition/
(fixed in version 1.2.4) - CVE-2024-28253 (CVSS score: 8.8) – A SpEL injection vulnerability in PUT /api/v1/policies (fixed in version 1.3.1)
- CVE-2024-28254 (CVSS score: 8.8) – A SpEL injection vulnerability in GET /api/v1/events/subscriptions/validation/condition/
(fixed in version 1.2.4) - CVE-2024-28255 (CVSS score: 9.8) – An authentication bypass vulnerability (fixed in version 1.2.4)
Successful exploitation of the vulnerabilities could allow a threat actor to bypass authentication and achieve remote code execution.
The modus operandi uncovered by Microsoft entails the targeting of internet-exposed OpenMetadata workloads that have been left unpatched to gain code execution on the container running the OpenMetadata image.
Upon gaining an initial foothold, the threat actors have been observed carrying out reconnaissance activities to determine their level of access to the compromised environment and gather details about the network and hardware configuration, operating system version, the number of active users, and the environment variables.
“This reconnaissance step often involves contacting a publicly available service,” security researchers Hagai Ran Kestenberg and Yossi Weizman said.
“In this specific attack, the attackers send ping requests to domains that end with oast[.]me and oast[.]pro, which are associated with Interactsh, an open-source tool for detecting out-of-band interactions.”
In doing so, the idea is to validate network connectivity from the infiltrated system to attacker-controlled infrastructure without raising any red flags, thereby giving threat actors the confidence to establish command-and-control (C2) communications and deploy additional payloads.
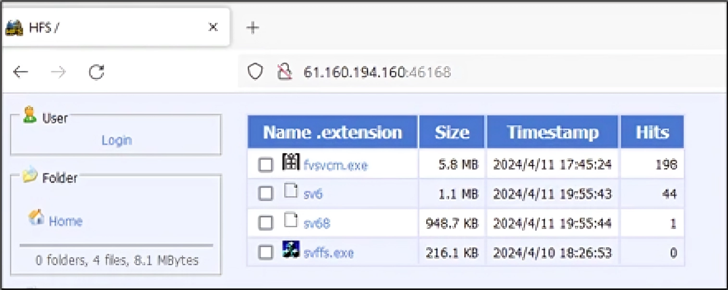
The end goal of the attacks is to retrieve and deploy a Windows or Linux variant of the crypto-mining malware from a remote server located in China, depending on the operating system.
Once the miner is launched, the initial payloads are removed from the workload, and the attackers initiate a reverse shell for their remote server using the Netcat tool, permitting them to commandeer the system. Persistence is achieved by setting cron jobs to run the malicious code at predefined intervals.
Interestingly, the threat actor also leaves behind a personal note telling that they are poor and that they need the money to buy a car and a suite. “I don’t want to do anything illegal,” the note reads.
OpenMetadata users are advised to switch to strong authentication methods, avoid using default credentials, and update their images to the latest version.
“This attack serves as a valuable reminder of why it’s crucial to stay compliant and run fully patched workloads in containerized environments,” the researchers said.
The development comes as publicly accessible Redis servers that have the authentication feature disabled or have unpatched flaws are being targeted to install Metasploit Meterpreter payloads for post-exploitation.
“When Metasploit is installed, the threat actor can take control of the infected system and also dominate the internal network of an organization using the various features offered by the malware,” the AhnLab Security Intelligence Center (ASEC) said.
It also follows a report from WithSecure that detailed how search permissions on Docker directories could be abused to achieve privilege escalation. It’s worth pointing out that the issue (CVE-2021-41091, CVSS score: 6.3) was previously flagged by CyberArk in February 2022, and addressed by Docker in version 20.10.9.
“The setting of the searchable bit for other users on /var/lib/docker/ and child directories can allow for a low-privileged attacker to gain access to various containers’ filesystems,” WithSecure said.